Saudi Arabia and the United Arab Emirates are currently weathering a sustained, sophisticated wave of cyber-attacks that go far beyond simple data theft. These operations represent a fundamental shift in regional gray-zone warfare, where the goal isn't just to steal secrets but to degrade the functional integrity of national infrastructure. While surface-level reports focus on the "who," the more pressing reality is the "how"—specifically the deployment of bespoke malware designed to bypass the multi-billion dollar security perimeters these nations have spent a decade building. This isn't a random surge in script-kiddie activity. It is a coordinated pressure campaign targeting the twin engines of the Middle East’s economic diversification.
The shift is palpable. For years, cyber threats in the Gulf were largely defined by crude "wiper" attacks or low-level espionage. Now, we see the emergence of persistent, quiet intruders that sit on networks for months, mapping out the physical dependencies of oil refineries, desalination plants, and smart-city grids. The attackers are no longer just looking for emails; they are looking for the valves, switches, and cooling systems that keep the lights on in Riyadh and Dubai.
The Illusion of the High Tech Fortress
There is a common misconception that throwing money at a problem solves it. Saudi Arabia and the UAE have some of the highest per-capita spending on cybersecurity in the world. They buy the best firewalls, hire the most expensive consultants, and build gleaming "Sovereign Clouds." Yet, they remain uniquely vulnerable.
This vulnerability stems from the very thing that makes them successful: rapid, top-down modernization. When you build a "giga-project" like NEOM or expand the digital footprint of ADNOC at breakneck speed, you create an enormous attack surface. Every internet-connected sensor in a smart building is a potential door. Every automated logistics hub is a target. The attackers aren't breaking the encryption; they are finding the one unpatched camera in a basement that provides a tunnel into the main server room.
We are seeing a move toward living-off-the-land techniques. In these scenarios, hackers don’t use obvious malware that triggers an alarm. Instead, they use the legitimate administrative tools already present in the system to move around. It makes the intruder look like an authorized employee. By the time the security team realizes something is wrong, the "employee" has already cloned the administrator credentials and established five different ways back into the system.
The Geopolitical Chessboard
It would be naive to view these attacks through a purely criminal lens. While ransomware gangs do operate in the region, the most sophisticated hits bear the hallmarks of state-sponsored or state-aligned groups. The timing often aligns perfectly with shifts in regional diplomacy or oil production quotas.
The Gulf is currently trying to play a delicate balancing act between Western security partnerships and Eastern economic ties. This "middle path" creates friction. Cyber-attacks serve as a low-cost, high-deniability way for rival powers to send a message. If a refinery’s control system glitches for four hours, it doesn’t trigger a war, but it does send a shudder through the global energy market. It is a reminder that the physical world is now entirely dependent on a digital layer that is surprisingly fragile.
Consider the recent focus on supply chain compromises. Rather than attacking a government ministry directly, hackers target the third-party software vendors that provide the ministry's payroll or maintenance systems. The Gulf depends heavily on international contractors. This creates a massive, sprawling web of trust that is only as strong as its weakest link—which might be a small software house in a completely different country.
Why the Current Defense Strategy is Failing
The primary issue is a reliance on reactive defense. Most organizations in the region are set up to respond to an alert. If a red light flashes on a dashboard, they act. But the most dangerous threats don't flash red. They stay "below the noise," mimicking normal traffic patterns.
- Over-reliance on Automated Tools: AI-driven security platforms are marketed as a silver bullet. They aren't. They are excellent at catching known patterns but struggle with original, "zero-day" logic that a human attacker uses to pivot through a network.
- The Talent Gap: You can buy the software, but you can't easily buy 10,000 elite analysts. There is a massive shortage of local tier-three security experts who understand the specific operational technology (OT) used in oil and gas.
- Data Silos: In many regional bureaucracies, departments don't share threat intelligence effectively. If the Ministry of Finance sees a specific type of phishing attempt, the Ministry of Energy might not hear about it for weeks.
The Physical Risk to Infrastructure
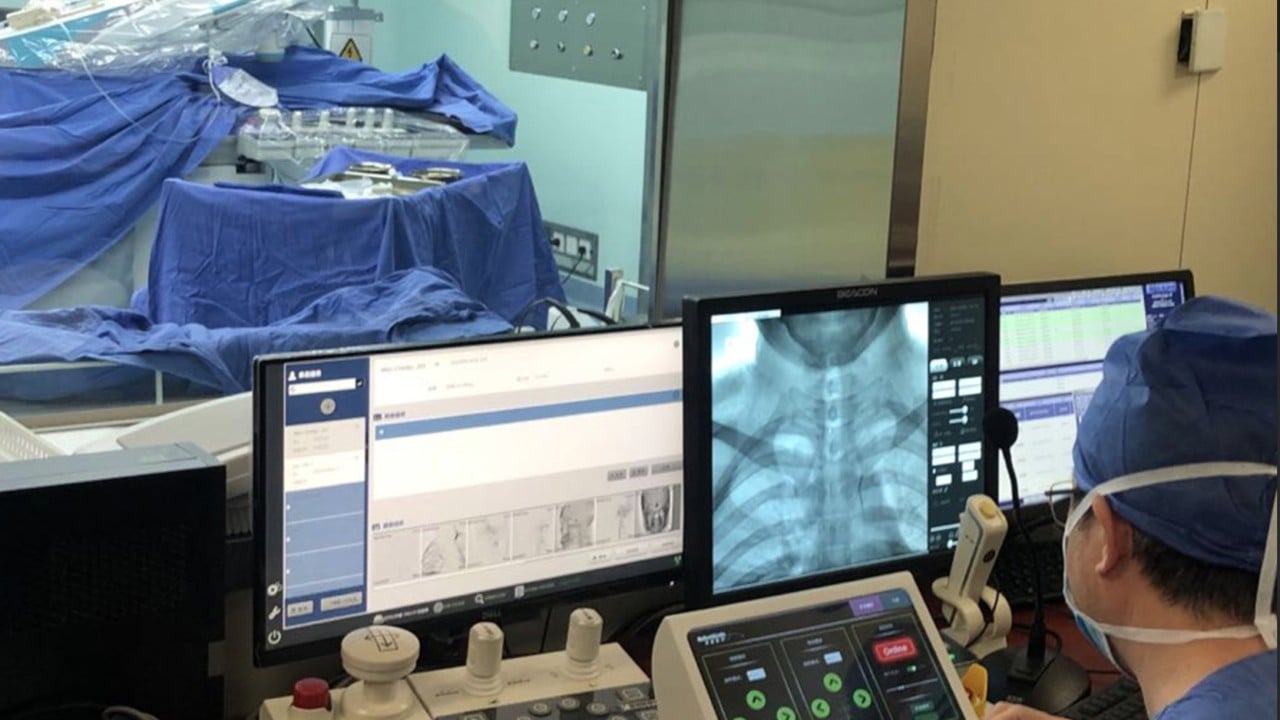
We have moved past the era of stolen credit cards. The current target is Industrial Control Systems (ICS). This is where the digital world meets the physical world.
If an attacker gains access to a Programmable Logic Controller (PLC) at a water treatment plant, they don't need to steal data. They can simply change the chemical levels in the water or shut down the pumps. In the harsh climate of the Arabian Peninsula, where water security is a matter of life and death, this is the ultimate nightmare scenario.
There is evidence that recent probes have specifically targeted the safety instrumented systems (SIS) of energy facilities. These are the systems designed to prevent explosions or catastrophic failures. When a hacker targets the "brakes" of a refinery, their intent is clearly more than just financial gain. It is an attempt to create the potential for physical destruction.
The Rise of the Hactivist Proxy
A new and complicating factor is the rise of "hactivist" groups that claim to be independent but clearly possess professional-grade tools. These groups often use social media to drum up publicity for their "operations," creating a sense of chaos and instability.
They use simple but effective tactics like Distributed Denial of Service (DDoS) attacks to knock government portals offline. While these don't cause long-term damage, they damage public trust. If a citizen can't access their government ID portal or their banking app for 24 hours, the narrative of a "seamless digital future" begins to crack. This psychological warfare is just as important to the attackers as the technical side.
Technical Sophistication and the Zero-Day Market
The Middle East has become a primary testing ground for high-end surveillance and intrusion software. There is a thriving "gray market" for zero-day exploits—vulnerabilities that the software creator doesn't know about yet.
A single exploit for an iPhone or a specific piece of industrial software can fetch millions of dollars. For wealthy regional actors and their adversaries, these are essential munitions. We are seeing "exploit chains" where multiple vulnerabilities are used in sequence to jump from a simple office computer all the way into the highly secure "air-gapped" networks that control critical machinery.
The assumption that a network is safe because it isn't connected to the public internet is a dangerous myth. There are numerous ways to bridge that gap, from compromised USB drives to "poisoned" software updates that an admin carries in on a laptop.
The Cost of Silence
One of the biggest hurdles to a real defense is the culture of secrecy. Many organizations in the Saudi and UAE markets are hesitant to admit they have been breached. They fear the reputational damage and the potential loss of investor confidence.
However, this silence only helps the attackers. When a breach is kept quiet, other organizations can't learn from the tactics used. It prevents the creation of a collective defense. The "threat actors"—to use the industry jargon—are constantly sharing information, techniques, and stolen credentials with each other. The defenders, meanwhile, are working in silos.
The shift toward mandatory breach reporting is a start, but it needs to go further. There needs to be a real-time, cross-border exchange of technical data that transcends political rivalries.
A New Framework for Survival
Fixing this requires more than just another "Vision" document or a new cabinet-level position. It requires a fundamental change in how digital risk is perceived at the board level.
- Assume Compromise: Stop building walls and start assuming the enemy is already inside. This means focusing on "internal" security—monitoring how data moves between departments, not just how it enters from the outside.
- Segment Everything: The "flat network" is a relic of the past. If a hacker gets into the guest Wi-Fi of a hotel, they should have zero path toward the elevator controls or the power grid.
- Invest in Human Hunting: You need "threat hunters"—people whose entire job is to look for the anomalies that the automated systems miss. These are the digital detectives who find the one "authorized" user logging in at 3:00 AM from a location they've never been to.
The attacks on Saudi Arabia and the UAE are a glimpse into the future of global conflict. In this world, the line between a civilian business and a military target is non-existent. The "front line" is every smartphone, every server, and every automated valve.
Winning this fight isn't about achieving "perfect security"—which is an impossible goal—but about achieving resilience. It's about being able to take a hit, isolate the damage, and keep the country running. For the Gulf powers, the ability to protect their digital nervous system is now just as important as the size of their air force or the price of a barrel of oil.
Audit your third-party access immediately. Most breaches don't happen because your security is bad; they happen because your partner's security is worse. Check every single vendor that has a "permanent" connection to your network and cut the ones that aren't strictly necessary.