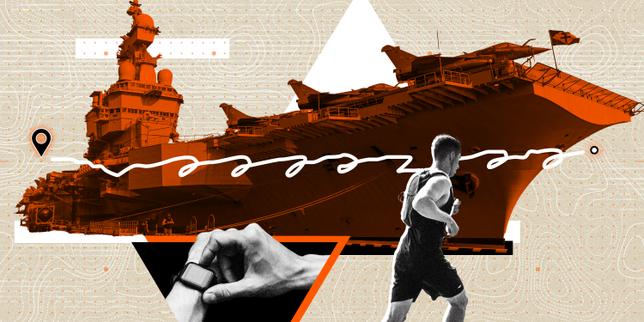
The recent exposure of the French aircraft carrier Charles-de-Gaulle through Strava data is not a failure of encryption or a breach of classified databases. It is a failure of Spatial Metadata Aggregation. When individual behaviors are digitized and uploaded to a central repository, the resulting dataset creates a high-fidelity thermal map of movement that can bypass traditional electronic warfare countermeasures. This incident serves as a definitive case study in how consumer-grade technology creates a persistent, unencrypted "leak" of state-level strategic assets.
The Triad of Digital Vulnerability
The compromise of the Charles-de-Gaulle rests on three distinct technical pillars that transform a fitness app into an unintentional intelligence-gathering tool.
- Identity Persistence: Every device has a unique identifier linked to a user profile. Even if the profile is "private," the movement data often remains part of an anonymized global heatmap.
- Geographic Specificity: GPS coordinates are absolute. While a ship’s position is dynamic, the "density of activity" in a specific coordinate at sea provides a signature that can only belong to a large vessel.
- Temporal Consistency: By tracking the routine of a single sailor or officer over weeks, an analyst can determine deployment cycles, port call durations, and even internal deck layouts.
Military operational security (OPSEC) has historically focused on blocking active transmissions—radio silence, radar jamming, and satellite obfuscation. However, these methods are ineffective against Passive Data Exhaust. The crew of the Charles-de-Gaulle provided the telemetry themselves, one morning run at a time.
The Signal-to-Noise Paradox
Standard counter-intelligence assumes that a small signal in a large dataset is "noise." In the context of maritime operations, the opposite is true. On the open ocean, the baseline for fitness activity is zero. Any cluster of GPS pings moving at 20-30 knots in the Mediterranean or the Atlantic becomes a statistically significant anomaly.
Le Monde utilized this paradox to identify the carrier’s position. By filtering the Strava Global Heatmap for high-velocity clusters in maritime zones, the carrier’s deck becomes a literal beacon. The "noise" of sailors running laps on the flight deck provides a high-resolution outline of the ship's geometry.
Mapping the Mechanism of Leakage
The path from a wearable device to a front-page headline follows a predictable logic chain:
- Data Generation: A sailor activates a "Run" or "Walk" activity on a smartwatch.
- Local Synchronization: The device syncs with a smartphone via Bluetooth.
- Cloud Ingestion: The smartphone uploads the data to Strava’s servers via cellular or satellite internet (often during port calls or via onboard Wi-Fi).
- Aggregated Visualization: Strava’s "Heatmap" feature processes this data to show popular routes.
- Open Source Intelligence (OSINT) Extraction: Analysts cross-reference the heatmap with known satellite imagery and AIS (Automatic Identification System) data to confirm the asset's identity.
Structural Failures in Personal Device Policies
The core of the problem is the Bifurcation of Security Responsibility. Military commands often regulate "official" hardware while treating personal devices as "private property." This creates a massive hole in the defensive perimeter.
The Charles-de-Gaulle incident demonstrates that a single individual’s privacy setting is irrelevant when the Aggregate Signature is public. Even if 99% of a crew disables tracking, the remaining 1% provides enough data points to triangulate the ship’s position. This is the Security of the Smallest Sample. In a high-stakes environment, the risk is not distributed; it is concentrated in the least-disciplined user.
Categorizing the Information Leakage
The data leaked through Strava can be categorized into three levels of severity:
- Tactical (Real-time Position): Knowing where the carrier is at a specific moment.
- Operational (Movement Patterns): Understanding the typical patrol routes and response times.
- Strategic (Personnel Profiling): Identifying specific high-ranking officers and tracking their movements back to their homes or sensitive land-based facilities.
The third category—Strategic Profiling—is the most dangerous. By following the "digital breadcrumbs" of an officer from the ship to a base in Toulon and then to a private residence, foreign intelligence services can build a comprehensive target list for recruitment, surveillance, or kinetic action.
The Cost Function of Modern OPSEC
Maintaining operational secrecy now requires an exponential increase in resources. In the 20th century, secrecy was a byproduct of physical distance and limited communications. In 2026, secrecy is a hard-fought state that must be actively maintained against the "gravity" of the internet.
The Incentive Gap remains the primary obstacle. Strava and similar platforms are built on social validation and competition—features that encourage users to share as much data as possible. These platforms are designed to be "sticky" and "open." Military environments, by definition, must be "rigid" and "closed." These two philosophies are in direct conflict.
Quantifying the Risk of Wearable Telemetry
To understand the scale, consider the data density of a single 30-minute run. A GPS device records location every 1-5 seconds. This generates approximately 360 to 1,800 data points per activity. On a vessel with a crew of 2,000, if only 50 people use tracking apps, the daily output exceeds 50,000 data points. This is more than enough to reconstruct the ship's daily operations with sub-meter accuracy.
The Failure of "Geofencing" as a Solution
A common suggestion is for Strava to "geofence" sensitive areas, such as naval bases or moving carriers. This approach is fundamentally flawed for two reasons:
- The "Hole in the Donut" Effect: If a tech company redacts data from a specific coordinate, the absence of data becomes a signal in itself. An empty square in a sea of data is as conspicuous as a bright light.
- Dynamic Geofencing Complexity: Unlike a stationary base, an aircraft carrier is a "floating city." Redacting a moving target in real-time requires the tech company to have access to the carrier’s classified location data—a circular logic that creates a secondary security risk.
The Institutional Bottleneck
The French Navy, like many global military organizations, faces an institutional bottleneck in reacting to rapid technological shifts. The delay between the emergence of a new data-sharing feature and the implementation of a restrictive policy is often measured in years. During this lag, the "data debt" accumulates. Once a run is uploaded, it exists in the archive forever. Even if a sailor deletes their account today, the historical heatmap data may already be cached by third-party scrapers or state-sponsored intelligence collectors.
Strategic Realignment: The Zero-Device Mandate
The only effective response to the StravaLeaks phenomenon is a shift from "Managed Use" to "Total Signal Suppression."
Military leadership must treat personal wearables as Passive Beacons. The strategy should shift toward the following operational requirements:
- Hardware Interdiction: Mandating the removal of all GPS-enabled personal devices during sensitive deployments. This is not a request; it is a fundamental requirement of mission integrity.
- Signal Scrambling and Spoofing: Developing "noise generation" tools that create thousands of fake fitness pings in random locations to dilute the actual signal of the fleet.
- Digital Hygiene as a Performance Metric: Integrating personal data security into the promotion and review process for service members.
The Charles-de-Gaulle incident is a warning. The next conflict will be fought in a world where the physical and digital are inseparable. If a state cannot control the "data exhaust" of its own soldiers, it has already lost the advantage of surprise. The objective is no longer to hide the ship; it is to hide the data generated by the people on the ship.
Commands must implement a Signal Audit immediately. Every deployment must begin with a sweep not just for physical stowaways, but for digital ones. The flight deck of a carrier is a place of immense power, but in the view of a global heatmap, it is just a collection of coordinates that need to be silenced.
The strategic play is to decouple the individual's desire for "fitness tracking" from the state's requirement for "survival." Until that happens, the most sophisticated aircraft carrier in the European fleet will continue to be tracked by a $200 watch.